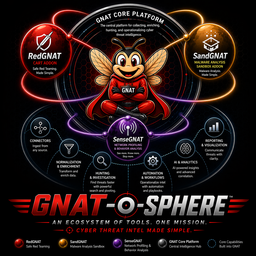
SenseGNAT
Network Profiling & Behavioral Analysis
Surface anomalies. Enrich investigations. Close the traffic-layer gap.
Indicator-based detection has a blind spot
- Known-bad indicators are only useful when you already know what you're looking for
- Novel infrastructure, fresh domains, and living-off-the-land techniques don't match existing IOCs
- Adversaries change indicators faster than threat intel feeds update
- Traffic-layer behavior often reveals compromise before any indicator is published
The behavioral gap
Indicator matching tells you what you already know is bad. Behavioral profiling tells you what is behaving badly — regardless of whether an indicator for it exists yet.
Network profiling & anomaly detection
- Baseline normal — profile the traffic patterns that represent normal behavior for your environment
- Surface anomalies — flag deviations from baseline: unusual beaconing, unexpected laterals, rare protocol usage
- Enrich GNAT investigations — publish findings back to the investigation graph automatically
- Consume raw telemetry via Kafka — integrates with the GNAT telemetry plane, not a separate pipeline
Traffic-layer context
SenseGNAT adds what indicator feeds can't: the behavioral picture of what's happening on the wire, in the context of what's known to be normal for your specific environment.
Built on the GNAT telemetry plane
Behaviors, not just indicators
Beaconing
Periodic outbound connections inconsistent with the host's established baseline. C2 traffic before the domain is in any feed.
Lateral Movement
Unexpected east-west traffic patterns — hosts communicating in ways that deviate from their normal peer groups.
Protocol Anomalies
Rare or unusual protocol usage from hosts that have no established pattern for that protocol.
Volume & Timing
Data exfiltration patterns: unusual outbound volumes, off-hours transfers, compressed transfer windows.
New Infrastructure
First-seen destinations, freshly registered domains, IP ranges with no prior relationship to your environment.
Peer Deviation
Hosts whose traffic profile diverges from their peer group — workstations behaving like servers, servers acting like endpoints.
Findings flow into the investigation automatically
- GNAT routes raw telemetry to the Kafka telemetry plane
- SenseGNAT consumes the stream and builds behavioral profiles
- Anomalies are detected against the environment-specific baseline
- Findings are published back to GNAT as STIX relationship objects
- The investigation graph receives behavioral context alongside indicator enrichment
- Analyst sees the full picture — IOCs plus behavioral signals — in one workspace
See what isn't in the feeds yet
- Behavioral signals arrive in your investigation graph alongside IOC enrichment
- No context-switching to a separate network analytics console
- Anomalies come with environmental context — not just a score, but a comparison to this host's established baseline
- First-seen infrastructure surfaces as a signal before it appears in any feed
- Pivot from a behavioral anomaly to related indicators, campaigns, and infrastructure in the same graph
One pipeline. Shared transport.
- SenseGNAT consumes from the existing GNAT Kafka telemetry plane — no separate ingestion pipeline
- Findings published back as STIX — same output format as everything else in the ecosystem
- Environment-specific baseline is built and maintained by SenseGNAT — no manual tuning of generic rules
- Open-source — read the profiling logic, tune it for your environment, contribute improvements
Getting started with SenseGNAT
- Have GNAT core deployed with the Kafka telemetry plane active
- Deploy SenseGNAT and point it at the
gnat.telemetrytopic - Let SenseGNAT build an environmental baseline — typically 7–14 days of representative traffic
- Review initial anomaly findings and tune the sensitivity to your environment
- Behavioral findings will begin appearing in GNAT investigation graphs automatically