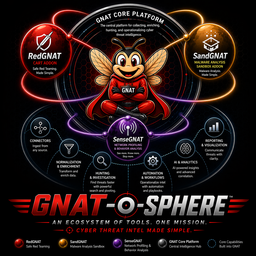
GNAT
GNAT's Not A TIP — Core Platform Deep Dive
Ingest · Normalize · Investigate · Export
Not a TIP. Not a SIEM. Not a replacement.
What GNAT is
- An investigation & workflow platform built around a connector surface
- A STIX-native normalization layer between your sources and your analysis
- A routing hub for the GNAT-o-sphere addons
- An open-source alternative to custom integration plumbing
What GNAT isn't
- A threat intelligence platform trying to replace your TIP
- A SIEM or log aggregation layer
- A vendor lock-in — STIX 2.1 output travels without GNAT
Every source is a custom integration
- Threat intel arrives from feeds, APIs, SIEMs, sandboxes, ISACs, and vendors — each with a different format
- Normalizing that data manually consumes analyst hours that should go to analysis
- One API change upstream breaks something downstream
- Workflows written against raw vendor data don't survive a vendor switch
159 connectors. One operating model.
- External feeds — OSINT, commercial, ISAC, government
- Platform APIs — SIEMs, TIPs, ticketing, case management
- Enrichment services — WHOIS, passive DNS, sandbox results
- Internal sources — EDR telemetry, network flows, endpoint logs
One framework to maintain
Every connector follows the same interface contract. Add a source once. Schema changes upstream are handled at the connector layer — your workflows see consistent STIX output regardless of what the vendor changes.
159 connectors. The stack you already use.
Threat Intel Platforms (24)
CrowdStrike Falcon · Recorded Future · Mandiant · MISP · OpenCTI · Anomali ThreatStream · VirusTotal · AlienVault OTX · Microsoft Defender TI · ThreatConnect · Cisco Talos · MITRE ATT&CK · Abuse.ch · AbuseIPDB · Intel 471 · Flashpoint · Group-IB · ZeroFox · SOCRadar · Pulsedive · +4 more
SIEM & Log Analytics (12)
Splunk Enterprise · Microsoft Sentinel · Elastic SIEM · IBM QRadar · Google Chronicle · Wazuh · LogRhythm · Graylog · OSSIM · Security Onion · Datadog SIEM · Cribl Stream
Endpoint & EDR (20)
SentinelOne · CrowdStrike (via TI) · VMware Carbon Black · Trellix XDR · Sophos Central · Tanium · Trend Micro Vision One · Fortinet FortiEDR · FortiSIEM · Shodan · GreyNoise · CISA KEV · Armis · Axonius · Claroty · Stellar Cyber · Netskope · +3 more
SOAR & Incident Response (7)
Palo Alto XSOAR · TheHive · GreyMatter · FortiSOAR · ServiceNow ITSM · ServiceNow SecOps · Atlassian Jira
Network Detection (9)
Zeek · Suricata IDS/IPS · Snort · Vectra AI · ExtraHop Reveal(x) · Darktrace · Cisco Umbrella · Nozomi Networks · Dragos Platform
Cloud & ASM (16)
Wiz · AWS Security Hub · Censys · Shodan · Palo Alto Prisma Cloud · Cortex Xpanse · Orca Security · CyCognito · SecurityTrails · DomainTools Iris · RiskRecon · BitSight · UpGuard · JupiterOne · runZero · Silent Push
Vuln Management (8)
Tenable One · Rapid7 InsightVM · Qualys VMDR · Greenbone/OpenVAS · Nucleus Security · DefectDojo · OSV.dev · VulnCheck
Identity & ITDR (5)
Okta · Microsoft Entra ID · Ping Identity · Silverfort · Semperis DSP
Malware Sandboxes (6) + More
ANY.RUN · Joe Sandbox · Hybrid Analysis · VMRay · Intezer · Cuckoo · MDR (Huntress, Arctic Wolf, Red Canary) · Email Security · Insider Risk · DFIR · BAS · DevSecOps
STIX 2.1 — the stable contract
- Vendor-neutral — not owned by any vendor, not tied to GNAT
- Relationship-aware — expresses connections between indicators, actors, TTPs, and campaigns as first-class objects
- Machine-readable — structured JSON bundles that tools can consume without manual parsing
- Portable — your STIX bundles travel. Export them, archive them, share them.
Why it matters
When everything GNAT produces is STIX 2.1, your workflows aren't tied to GNAT. If you change tools, your structured intelligence output doesn't disappear with your old platform.
Repeatable investigations, not one-off hunts
- Ingest indicators from one or many connectors
- Normalize to STIX — relationships, context, and metadata preserved
- Route artifacts to addons (SenseGNAT, SandGNAT, RedGNAT) as needed
- Correlate findings in the investigation graph — enrich, pivot, annotate
- Produce structured output: STIX bundles, reports, case export
From raw indicator to connected evidence
- Visualize relationships between indicators, actors, infrastructure, and campaigns
- Pivot from an IP to associated domains, ASNs, and malware samples
- Annotate nodes with analyst findings and link to source evidence
- Add enrichment from addons — detonation results, behavioral profiles, validation outcomes
- Export the full graph as a STIX bundle or structured report
Not a dashboard
The investigation graph is an active workspace — you build the picture as the investigation progresses. It's not a static visualization of pre-ingested data.
GNAT as the routing hub
What leaves GNAT travels independently
STIX 2.1 Bundles
Machine-readable, vendor-neutral. Share with any STIX-compatible platform, archive for recall, or feed downstream tools automatically.
Structured Reports
Human-readable reports generated from investigation graph data. Consistent format across every investigation, not rebuilt from scratch each time.
Case Export
Push case data to ticketing, SOAR, or case management. The investigation record doesn't stay locked inside the platform.
Less plumbing. More analysis.
- Feeds are already normalized when you start an investigation — no pre-work
- The graph builds as you pivot — context accumulates in one place
- Workflow templates encode your investigation methodology so you can run it, not rebuild it
- Enrichment from addons lands in the investigation automatically
- Reports come from the graph — not from a separate document written after the fact
One framework. Not 159 scripts.
- Write one connector interface — all 159 sources follow the same pattern
- API changes upstream are handled at the connector layer — workflows downstream see stable STIX
- Addon routing is configuration, not code — change where artifacts go without rewriting logic
- STIX 2.1 output integrates cleanly with any downstream tool that speaks the standard
- Open-source — read the code, fork it, contribute connectors for your environment
Durable investment. Portable output.
- No vendor lock-in — STIX 2.1 output lives independently of GNAT
- Incremental adoption — start with GNAT core, add addons when ready
- Open-source — no licensing cost, full access to the code
- Team leverage — analyst workflows encoded in the platform, not in individual knowledge
The durability argument
When your investigation workflow is a repeatable template backed by a vendor-neutral standard, it survives vendor changes, team changes, and tool changes. That's the investment you're making.
Getting started with GNAT
- Deploy GNAT core — open-source, self-hosted
- Connect your first sources — pick 2–3 feeds you already rely on
- Run your first investigation — one indicator, full pivot through the graph
- Build a workflow template from a real investigation you just completed
- Add addons as capability needs surface